Prerequisites
Docker, runs on Ubuntu, Mac OS X, and Windows
Introduction
ISSA Journal’s theme of the
month is “Malware and what to do with it”. This invites so many possible
smart-alecky responses, including where you can stick it, means by which to
smoke it, and a variety of other abuses for the plethora of malware authors
whose handy work we so enjoy each and every day of our security professional
lives. But alas, that won’t get us further than a few chuckles, so I’ll just
share the best summary response I’ve read to date, courtesy of @infosecjerk,
and move on.
“Security is easy:
1)
Don't install malicious software.
2)
Don't click bad stuff.
3)
Only trust pretty women you don't know.
4)
Do what Gartner says.”
Wait, now I’m not sure
there’s even a reason to continue here. :-)
One of the true benefits of
being a SANS Internet Storm Center Handler is working with top notch security
industry experts, and one such person is Lenny Zeltser. I’ve enjoyed Lenny’s
work for many years; if you’ve taken SANS training you’ve either heard of or
attended his GIAC Reverse Engineering Malware course and likely learned a great
deal. You’re hopefully also aware of Lenny’s Linux toolkit for reverse-engineering
and analyzing malware, REMnux. I covered REMnux in September 2010, but it, and
the landscape, have evolved so much in the five years since. Be sure to grab
the latest OVA and revisit it, if you haven’t utilized it lately. Rather than
revisit REMnux specifically this month, I’ll draw your attention to a really
slick way to analyze malware with Docker and specific malware-analysis related
REMnux project Docker containers that
Lenny’s created. Lenny expressed that he is personally interested in packaging
malware analysis apps as containers because it gives him the opportunity to
learn about container technologies and understand how they might be related to his
work, customers and hobbies. Lenny’s packaging tools that are “useful in a
malware analysis lab, that like-minded security professionals who work with
malware or forensics might also find an interesting starting point for
experimenting with containers and assessing their applicability to other
contexts.”
Docker can be utilized on
Ubuntu, Mac OS X, and Windows, I ran it on the SANS SIFT 3.0 virtual machine
distribution, as well as my Mac Mini. The advantage of Docker containers, per the
What Is Docker page, is simple to understand. First, “Docker allows you to
package an application with all of its dependencies into a standardized unit
for software development.” Everything you need therefore resides in a
container: “Containers have similar resource isolation and allocation benefits
as virtual machines but a different architectural approach allows them to be
much more portable and efficient.” The Docker Engine is just that, the source
from whom all container blessings flow. It utilizes Linux-specific kernel
features so to run it on Windows and Mac OS X, it will install VirtualBox and
boot2docker to create a Linux VM for the containers to run on Windows and Mac
OS X. Windows Server is soon adding direct support for Docker with Windows
Server Containers. In the meantime, if you’re going to go this extent, rather
than just run natively on Linux, you might as well treat yourself to Kitematic,
the desktop GUI for Docker. Read up on
Docker before proceeding if you aren’t already well informed. Most importantly,
read Security Risks and Benefits of Docker Application Containers.
Lenny mentioned that he is
not planning to use containers as the architecture for the REMnux distro,
stating that “This distribution has lots of useful tools installed directly on
the REMnux host alongside the OS. It's fine to run most tools this way.
However, I like the idea of being able to run some applications as separate
containers, which is certainly possible using Docker on top of a system running
the REMnux distro.” As an example, he struggled to set up Maltrieve and JSDetox
directly on REMnux without introducing dependencies and settings that might
break other tools but “running these applications as Docker containers allows
people to have access to these handy utilities without worrying about such
issues.” Lenny started the Docker image repository under the REMnux project umbrella
to provide people with “the opportunity to conveniently use the tools available
via the REMnux Docker repository even if they are not running REMnux.”
Before we dig in to REMnux
Docker containers, I wanted to treat you to a very cool idea I’ve implemented
after reading it on the SANS Digital Forensics and Incident Response Blog as
posted by Lenny. He describes methods to install REMnux on a SIFT workstation, or
SIFT on a REMnux workstation. I opted for the former because Docker runs really
cleanly and natively on SIFT as it is Ubuntu 14.04 x64 under the hood. Installing
REMnux on SIFT is as easy as wget
--quiet -O - https://remnux.org/get-remnux.sh | sudo bash, then wait a
bit. The script will update APT repositories (yes, we’re talking about malware
analysis but no, not that APT) and install all the REMnux packages. When
finished you’ll have all the power of SIFT and REMnux on one glorious
workstation. By the way, if you want to use the full REMnux distribution as
your Docker host, Docker is already fully installed.
Docker setup
After you’ve squared away
your preferred distribution, be sure to run sudo
apt-get update && sudo apt-get upgrade, then run sudo apt-get install docker.io.
REMnux Docker Containers
Included in the REMnux
container collection as of this writing you will find the
V8 JavaScript engine, the Thug low-interaction
honeyclient, the Viper binary analysis framework, Rekall and
Volatility memory forensic
frameworks, the JSDetox JavaScript analysis tool, the Radare2 reverse engineering
framework, the Pescanner static malware analysis tool, the MASTIFF static analysis
framework, and the Maltrieve malware samples downloader. This may well give you
everything you possibly need as a great start for malware reverse engineering
and analysis in one collection of Docker containers. I won’t discuss the Rekall
or Volatility containers as toolsmith readers should already be intimately
familiar with, and happily using, those tools. But it is mighty convenient to
know you can spin them up via Docker.
The first time you run a
Docker container it will be automatically pulled down from the Docker Hub if
you don’t already have a local copy. All the REMnux containers reside there,
you can, as I did, start with @kylemaxwell’s wicked good Maltrieve by executing
sudo docker run --rm -it
remnux/maltrieve bash. Once the container is downloaded and ready, exit
and rerun it with sudo docker run --rm
-it -v ~/samples:/home/sansforensics/samples remnux/maltrieve bash after
you build a samples directory in your home directory. Important note: the -v parameter defines a shared
directory that the container and the supporting host can both access and
utilized. Liken it to Shared Folders in VMWare. Be sure to run sudo chmod a+xwr against it so it’s
world readable/writeable. When all said and done you should be dropped to a
nonroot prompt (a good thing), simply run maltrieve
-d /home/sansforensics/samples/ -l /home/sansforensics/samples/maltieve.log
and wait again as it populates malware samples to your sample directory, as
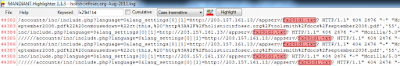
seen in Figure 1, from the likes of Malc0de, Malware Domain List, Malware URLs,
VX Vault, URLquery, CleanMX, and ZeusTracker.
 |
| Figure 1 – Maltrieve completes its downloads, 780 delicious samples ready for REMnux |
So nice to have a current
local collection. The above mentioned sources update regularly so you can keep
your sample farm fresh. You can also define your preferred DUMPDIR and log
directories in maltrieve.cfg for ease of use.
Next up, a look at the REMnux
MASTIFF container. “MASTIFF is a static analysis framework that automates the
process of extracting key characteristics from a number of different file
formats” from @SecShoggoth.
I ran it as follows: sudo docker run --dns=my.dns.server.ip --rm
-it -v ~/samples:/home/sansforensics/samples remnux/mastiff bash. You
may want or need to replace --dns=my.dns.server.ip
with your preferred DNS
server if you don’t want to use the default 8.8.8.8. I found this ensured name
resolution for me from inside the container. MASTIFF can call the VirusTotal
API and submit malware if you configure it to do so with mastiff.conf, it will
fail if DNS isn’t working properly. You need to edit mastiff.conf via vi with you API key and enable submit=yes. Also note that, when invoked with --rm parameters, the container will be ephemeral and all
customization will disappear once the container exits. You can invoke the
container differently to save the customization and the state.
You may want to also instruct the log_dir
directive to point at your shared samples directory so the results are written
outside the container.
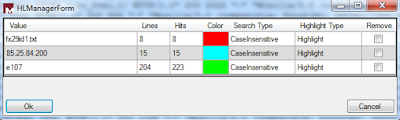
You can then run mas.py
/your/working/directory/samplename with your correct preferences and the result should resemble
Figure 2.
 |
| Figure 2 – Successful REMnux MASTIFF run |
All of the results can be found in /workdir/log under a folder named for each sample analyzed. Checking the
Yara results in yara.txt will inform you that the while the payload is a PE32 it
exhibits malicious document attributes per Didier Steven’s (another brilliant
Internet Storm Center handler) maldoc rules as seen in Figure 3.
 |
| Figure 3 – Yara results indicating a malicious document attributes |
The peinfo-full and peinfo-quick results will provide further
details, indicators, and behaviors necessary to complete your analysis.
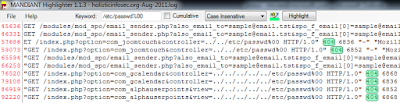
Our last example is the REMnux JSDetox container. Per its
website, courtesy of @sven_t, JSDetox “is a tool to support the manual analysis
of malicious Javascript code.” To run it is as simple as sudo docker run --rm -p 3000:3000
remnux/jsdetox, then
point your browser to http://localhost:3000
on your container host system. One of my favorite obfuscated malicious
JavaScipt examples comes courtesy of aw-snap.info and is seen in its raw,
hidden ugliness in Figure 4.
 |
| Figure 4 – Obfuscated malicious JavaScript |
Feed said script to JSDetox
under the Code Analysis tab, run
Analyze, choose the Execution tab, then Show Code and you’ll quickly learn
that the obfuscated code serves up a malicious script from palwas.servehttp.com,
flagged by major browsers and Sucuri.net as distributing malware and acting as
a redirector. The results are evident in Figure 5.
 |
| Figure 5 – JSDetox results |
All the malware analysis horsepower you can imagine in the
convenience of Docker containers, running on top of SIFT with a full REMnux
install too. Way to go, Lenny, my journey is complete. J
In Conclusion
Lenny’s plans for the future include maintaining and
enhancing the REMnux distro with the help of the Debian package repository he
set up for this purpose with Docker and containers part of his design.
Independently, he will continue to build and catalog Docker containers for
useful malware analysis tools, so they can be utilized with or without the
REMnux distro. I am certain this is the best way possible for you readers to
immerse yourself in both Docker technology and some of the best of the REMnux
collection at the same time. Enjoy!
Ping me via email or Twitter if you have questions (russ
at holisticinfosec dot org or @holisticinfosec).
Cheers…until next month.
ACK
Thanks again to Lenny
Zeltser, @lennyzeltser, for years of REMnux, and these Docker containers.